Use an MCP gateway when Model Context Protocol needs policy, scope, and review.
A useful MCP gateway does more than expose tools. It keeps Model Context Protocol behind curated server catalogs, explicit org approval, per-key tool scope, and the same review path already used for AI Gateway policy and routing.
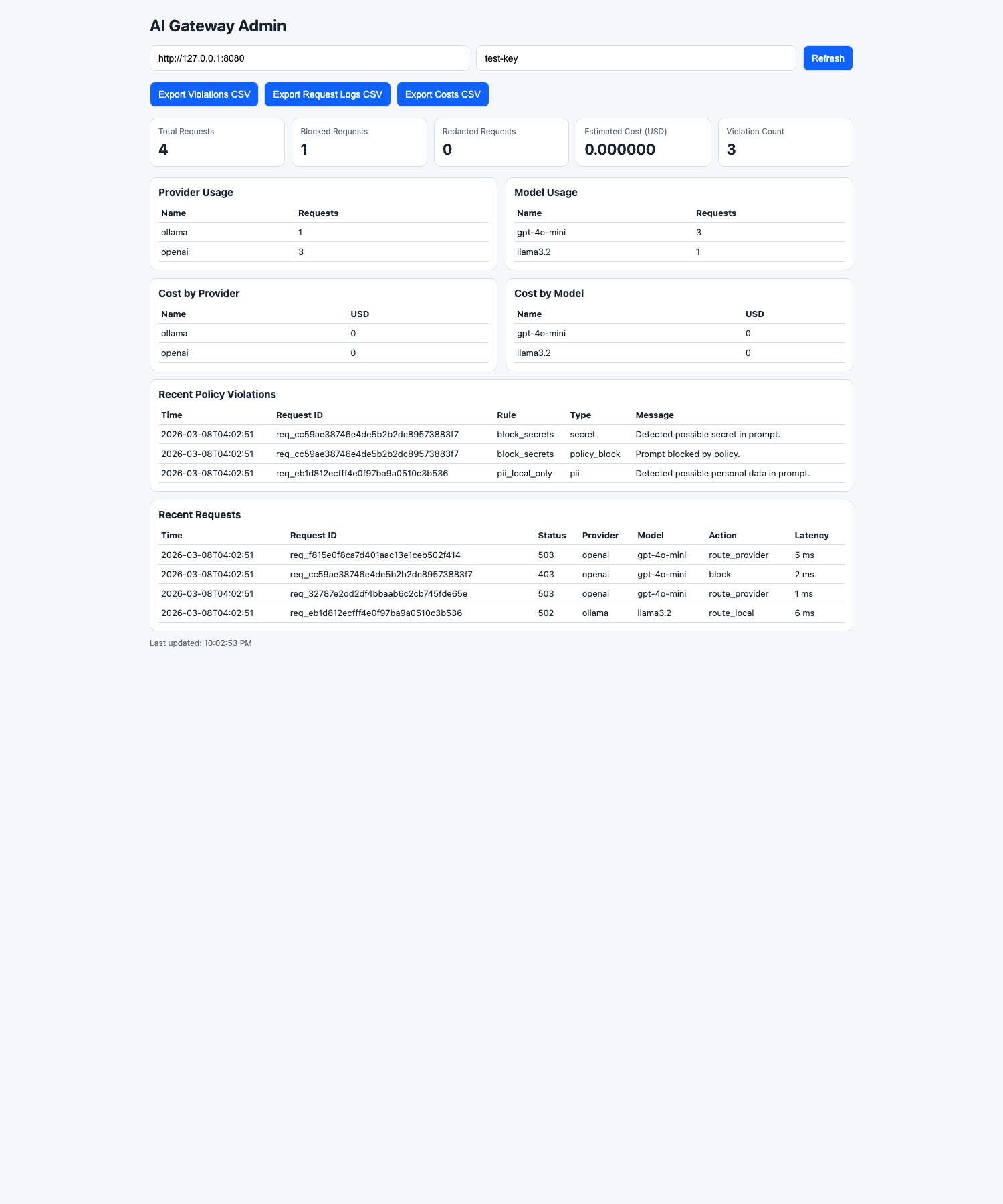
Posturio keeps MCP inside the same AI Gateway workflow instead of treating it as a parallel tunnel. That keeps tool approvals and traces visible across applications.
MCP gateway summary
What an MCP gateway adds beyond raw MCP support
Raw MCP support makes tools reachable. An MCP gateway decides which servers and tools should be reachable at all, which keys can use them, and what operators can review after a tool-backed request runs.
That matters because production requirements do not stop at protocol compatibility. Teams still need an approval model, review path, and day-two workflow that scales beyond one demo.
- Approve remote MCP servers before they are exposed to apps
- Sync tool catalogs into one shared request layer
- Enable tools intentionally at the org level
- Scope live keys down to narrower MCP tool sets
- Keep tool traces attached to request review
Why direct MCP adoption usually breaks down in production
Server sprawl
Apps start pointing at whichever MCP server solves the immediate task, then teams lose track of what is actually approved.
Scope drift
Without a shared access model, broad server approval and the narrower tool scope each workflow needs blur together.
No review path
Security and platform teams end up reconstructing tool behavior later because traces and blocked execution are not visible in one queue.
How Posturio governs MCP-backed requests today
- Curate remote MCP servers in one catalog instead of letting applications name arbitrary endpoints.
- Approve servers and tools at the organization level before any live key can use them.
- Narrow individual keys to smaller MCP tool allowlists where a workflow needs less than the full org scope.
- Suppress MCP execution when prompt inspection detects secrets, personal data, or prompt-injection signals.
- Keep redacted argument and result previews attached to request review and investigation records.
The gateway matters because production use still needs operators
Model Context Protocol becomes an enterprise buying question once platform and security teams need to understand what changed in the request path, which tool ran, and whether a blocked prompt reached the tool layer at all.
The current Posturio console already treats MCP as part of live key scope, policy review, and investigations rather than a separate product surface.