Architecture patterns for teams rolling out governed internal AI.
A useful AI gateway architecture has to do more than proxy requests. It needs to inspect prompts, enforce policy, route models, preserve operator visibility, and still give application teams an integration path they can adopt quickly.
This page shows the Posturio AI Gateway reference patterns the way a buyer or engineer actually evaluates them: request flow, hosted stack, deployment choices, and the day-two operator workflow behind the gateway.
Reference focus
Hosted AI Gateway reference stack
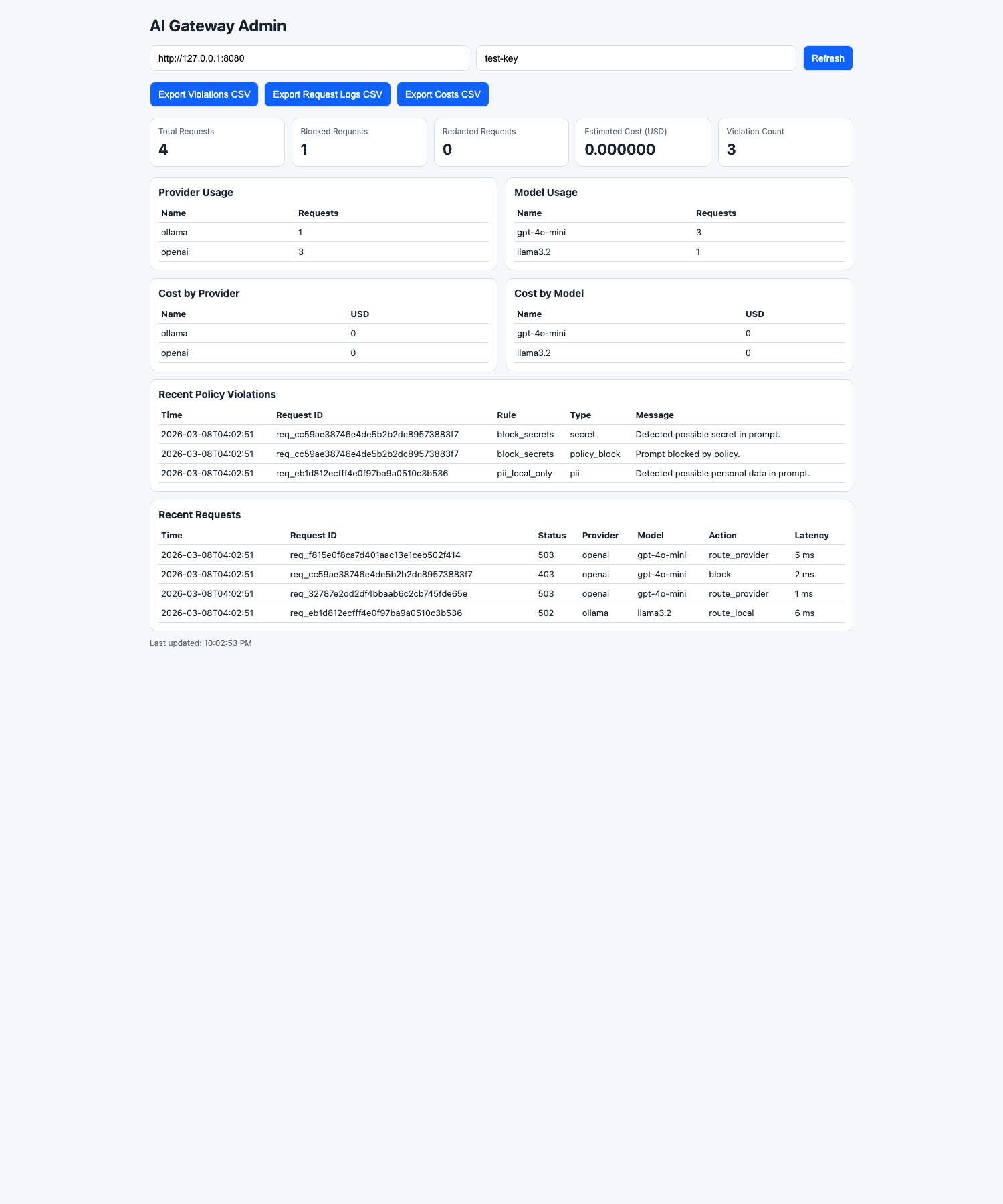
The current Posturio AI Gateway demo runs a direct request path from public product evaluation into live request inspection, policy enforcement, routing, managed MCP tool catalogs, and usage visibility. That matters because teams can validate real operator behavior before they commit to a deeper deployment.
api.posturio.co → reverse proxy / load balancer (HTTPS) → gateway container (FastAPI) → Postgres → Redis
Hosted signup, demo key issuance, browser playground, and a direct first request path on the product page.
Console review, demo key visibility, MCP tool governance, investigations, and saved workflow inside the shared Posturio console.
Three architecture patterns buyers usually separate
Hosted AI Gateway
Fastest way to validate OpenAI-compatible integration, prompt inspection, routing, managed MCP tools, and operator workflow against real internal prompts.
Self-hosted gateway path
Useful when infrastructure or security requirements demand tighter deployment control, but the team still needs routing and policy enforcement.
AI Gateway plus Navigator
Best when the gateway decision also affects grounded internal AI search, approved sources, managed MCP tools, and broader internal AI deployment.
What the control path actually does
- Receives OpenAI-compatible requests from internal tools, assistants, or browser evaluation flows.
- Inspects prompts before the upstream provider call.
- Blocks or reroutes requests when secrets, sensitive content, or policy conditions are triggered.
- Surfaces approved MCP tool catalogs through governed access instead of exposing arbitrary servers.
- Returns routing and gateway metadata so engineering and security can review what happened.
Signals worth validating in any AI gateway architecture review
Abuse protection
Challenge flow, proof-of-work, throttling, demo limits, and request-size controls show whether public evaluation traffic is treated as a real operating surface.
Policy review path
Blocked-request handling, investigation context, and reviewer workflow matter more than a simple allow-path demo.
Expansion path
The architecture decision should still make sense once the team adds more internal assistants, coding tools, or grounded search workflows.